- Google Cloud
- :
- Cloud Forums
- :
- Apigee
- :
- Re: Failing to generate JWT using a password prote...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not able to generate JWT using a password protected private key. I am getting following response:
{
"fault": {
"faultstring": "Failed to parse key: policy(Generate-JWT-Token) ",
"detail": {
"errorcode": "steps.jwt.KeyParsingFailed"
}
}
}I am not sure if the policy is able to consume the password protected private key in this case. I might be missing something here. Please help.
Here is my setup
1. I have generated PEM (password protected private key) using following command
openssl pkcs12 -in tokensigning.pfx -nocerts -out token-private-key.pem
Here is the encryption method details from PFX
openssl pkcs12 -info -in tokensigning.pfx -nooutPKCS7 Data Output: Shrouded Keybag: pbeWithSHA1And3-KeyTripleDES-CBC, Iteration 2000 PKCS7 Encrypted data: pbeWithSHA1And3-KeyTripleDES-CBC, Iteration 2000
Private Key
Bag Attributes
Microsoft Local Key set: <No Values>
localKeyID: 01 00 00 00
Microsoft CSP Name: Microsoft RSA SChannel Cryptographic Provider
friendlyName: some-friendly-name-16a8f7db122f
Key Attributes
X509v3 Key Usage: 10
-----BEGIN ENCRYPTED PRIVATE KEY-----
key data.......
-----END ENCRYPTED PRIVATE KEY-----
KeyValueMap Policy
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<KeyValueMapOperations name="KVM-GetTokenSigningPrivateKey" mapIdentifier="oauth-token-signing">
<Scope>environment</Scope>
<ExpiryTimeInSecs>15</ExpiryTimeInSecs>
<Get assignTo="private.private-key">
<Key>
<Parameter>privatekey</Parameter>
</Key>
</Get>
<Get assignTo="private.privatekey-password">
<Key>
<Parameter>privatekey-password</Parameter>
</Key>
</Get>
</KeyValueMapOperations>
Generate JWT policy
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<GenerateJWT name="Generate-JWT-Token">
<Algorithm>RS256</Algorithm>
<PrivateKey>
<Value ref="private.private-key"/>
<Password ref="private.privatekey-password"/>
<Id>unique-identifier-for-privatekey-here</Id>
</PrivateKey>
<Subject>ABCD</Subject>
<Issuer>urn://1a4b40567d5a</Issuer>
<Audience>urn://api.dev</Audience>
<ExpiresIn>60m</ExpiresIn>
<AdditionalClaims>
<Claim name="apigee-proxy" ref="apiproxy.name"/>
<Claim name="messageid" ref="messageid"/>
<Claim name="request-path" ref="request.path"/>
<Claim name="apigee-org" ref="organization.name"/>
<Claim name="apigee-env" ref="environment.name"/>
</AdditionalClaims>
<OutputVariable>output-jwt</OutputVariable>
</GenerateJWT>
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The GenerateJWT policy in Apigee Edge is pretty limited in the kind of encryption you can use on your private key. In short, you need to use DES-EDE3-CBC, today, and you need to use the old serialization format, which looks like this:
-----BEGIN RSA PRIVATE KEY----- Proc-Type: 4,ENCRYPTED DEK-Info: DES-EDE3-CBC,97B6E793909D97A345CB0CDBA89F8516 SyO+gWBhcwiqluLoETYkis1YkQsa7XiteXvsixgiu8NnQpOLbJc28WngSFc7Y0Qq pARMGGqFZbaFfP91LYmZQv37p5rlWllGpOqQudYCdEWjR+MMSZ7eqRcc2gDKSDAz +y7+0oYEkZG9qt1n2fkpsA_THIS_IS_NOT_A_REAL_KEY_87ctbqlW16fLM8fRbV eGtYP0nb24tq9ZtO47jzlcMvGy9WTfYRCZAuYeZfmQo4nlBoWrVK7c/0+jprvvna gmbQouafPH86qsC5UswSg7SuwFbReEiU25hPWxVN4BWoK7Yc/4lihFg/QLd+b6Zs dog8hj5bFdRYH2rOuV6gKj0FNmYAlfVOuclV9c8Z7h0DyC2oBmF0T3MCUyl0S0gZ -----END RSA PRIVATE KEY-----
As I type this, there is a release being rolled out to the Edge cloud that supports a wide variety of encryption algorithms. It also supports both the older serialization format, shown above, and the newer serialization format, which looks like this:
-----BEGIN ENCRYPTED PRIVATE KEY----- MIICXjBABgkqhkiG9w0BBQ0wMzAbBgkqhkiG9w0BBQwwDgQIH4x6YwuP+HICAggA MBQGCCqGSIb3DQMHBAifETAsGQulyASCAhhiYS2ZyhBNMh6zVzYZwUdTfWGwOXIU 0oEkZG9qt1n2fkpsA_THIS_IS_ALSO_NOT_A_REAL_KEY_87ctbqlW16fLM8fRbV gvaZfwfnWXGrBPmIZEdx8fL4NrfDHLs409BFAqWFgFPKyeJGTO9sIdpKjdRjD33X 8SxW+wORheOafjrZlLargzEDoA9cxuFglNcMXRyTp+0i3A/e9VU3OWCAG4j+xKAW NnvBAT+97XcpOu1DMHBiH8UOcrNxXFuR38MwU8EIT8eMzmAnw5yTNS+un+tPPzcD bDqOFr8NhZ9BYfxsQfu05mQwt6hgEPRDSoHVSTeyqWTUDw== -----END ENCRYPTED PRIVATE KEY-----
There are other changes coming to the JWT policies, and I've written about them in some detail, here.
This updated release is being rolled to Asia Pacific and EU now, north and south america soon. Check the status page for details and updates.
When this release becomes available for you, you must specify the key PEM in a form like the above. It should not have extraneous material like so:
Bag Attributes
Microsoft Local Key set: <No Values>
localKeyID: 01 00 00 00
Microsoft CSP Name: Microsoft RSA SChannel Cryptographic Provider
friendlyName: some-friendly-name-16a8f7db122f
Key Attributes
X509v3 Key Usage: 10
-----BEGIN ENCRYPTED PRIVATE KEY-----
key data.......
-----END ENCRYPTED PRIVATE KEY-----Just start with the header and end with the footer.
-----BEGIN ENCRYPTED PRIVATE KEY----- key data....... -----END ENCRYPTED PRIVATE KEY-----
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dino-at-Google, Any inputs on what I might be doing wrong here?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I guess the issue is with your private key. Maybe it is not supported in APigee
I have never used a private key which has BagAttributes.
Even I am waiting for Dino's answer in this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The GenerateJWT policy in Apigee Edge is pretty limited in the kind of encryption you can use on your private key. In short, you need to use DES-EDE3-CBC, today, and you need to use the old serialization format, which looks like this:
-----BEGIN RSA PRIVATE KEY----- Proc-Type: 4,ENCRYPTED DEK-Info: DES-EDE3-CBC,97B6E793909D97A345CB0CDBA89F8516 SyO+gWBhcwiqluLoETYkis1YkQsa7XiteXvsixgiu8NnQpOLbJc28WngSFc7Y0Qq pARMGGqFZbaFfP91LYmZQv37p5rlWllGpOqQudYCdEWjR+MMSZ7eqRcc2gDKSDAz +y7+0oYEkZG9qt1n2fkpsA_THIS_IS_NOT_A_REAL_KEY_87ctbqlW16fLM8fRbV eGtYP0nb24tq9ZtO47jzlcMvGy9WTfYRCZAuYeZfmQo4nlBoWrVK7c/0+jprvvna gmbQouafPH86qsC5UswSg7SuwFbReEiU25hPWxVN4BWoK7Yc/4lihFg/QLd+b6Zs dog8hj5bFdRYH2rOuV6gKj0FNmYAlfVOuclV9c8Z7h0DyC2oBmF0T3MCUyl0S0gZ -----END RSA PRIVATE KEY-----
As I type this, there is a release being rolled out to the Edge cloud that supports a wide variety of encryption algorithms. It also supports both the older serialization format, shown above, and the newer serialization format, which looks like this:
-----BEGIN ENCRYPTED PRIVATE KEY----- MIICXjBABgkqhkiG9w0BBQ0wMzAbBgkqhkiG9w0BBQwwDgQIH4x6YwuP+HICAggA MBQGCCqGSIb3DQMHBAifETAsGQulyASCAhhiYS2ZyhBNMh6zVzYZwUdTfWGwOXIU 0oEkZG9qt1n2fkpsA_THIS_IS_ALSO_NOT_A_REAL_KEY_87ctbqlW16fLM8fRbV gvaZfwfnWXGrBPmIZEdx8fL4NrfDHLs409BFAqWFgFPKyeJGTO9sIdpKjdRjD33X 8SxW+wORheOafjrZlLargzEDoA9cxuFglNcMXRyTp+0i3A/e9VU3OWCAG4j+xKAW NnvBAT+97XcpOu1DMHBiH8UOcrNxXFuR38MwU8EIT8eMzmAnw5yTNS+un+tPPzcD bDqOFr8NhZ9BYfxsQfu05mQwt6hgEPRDSoHVSTeyqWTUDw== -----END ENCRYPTED PRIVATE KEY-----
There are other changes coming to the JWT policies, and I've written about them in some detail, here.
This updated release is being rolled to Asia Pacific and EU now, north and south america soon. Check the status page for details and updates.
When this release becomes available for you, you must specify the key PEM in a form like the above. It should not have extraneous material like so:
Bag Attributes
Microsoft Local Key set: <No Values>
localKeyID: 01 00 00 00
Microsoft CSP Name: Microsoft RSA SChannel Cryptographic Provider
friendlyName: some-friendly-name-16a8f7db122f
Key Attributes
X509v3 Key Usage: 10
-----BEGIN ENCRYPTED PRIVATE KEY-----
key data.......
-----END ENCRYPTED PRIVATE KEY-----Just start with the header and end with the footer.
-----BEGIN ENCRYPTED PRIVATE KEY----- key data....... -----END ENCRYPTED PRIVATE KEY-----
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @Dino-at-Google, Good to know that new release is going to support additional algorithms and will have added security in place. I am eagerly waiting it to complete. Many thanks for taking time out for looking into my question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm glad to be of service, Amit!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @Dino-at-Google, Do you know by when this roll out to be completed in EU. I am seeing an erratic behavior. My endpoint which is reading a Encrypted Private Key works once in five tries. Is is something related to the roll-out?
-----BEGIN ENCRYPTED PRIVATE KEY----- key data....... -----END ENCRYPTED PRIVATE KEY-----
Please let me know if you would like me to raise this as a separate question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
@Dino-at-Google, colleagues,
today I try with all the instructions/best practices shared in this and similar posts, but it all fails.
1. I generate an encrypted DES-EDE3-CBC RS256 private key using password "1234" with this command:
openssl genrsa -des3 -out private-encrypted-rsa-des3.pem 2048
C:\Users\Rostislav_Dublin\IdeaProjects\osdu-epam\entitlements>openssl genrsa -des3 -out private-encrypted-rsa-des3.pem 2048 Generating RSA private key, 2048 bit long modulus (2 primes) ........................+++++ ............................+++++ e is 65537 (0x010001) Enter pass phrase for private-encrypted-rsa-des3.pem: Verifying - Enter pass phrase for private-encrypted-rsa-des3.pem:<br>
The resulting file is
-----BEGIN RSA PRIVATE KEY----- Proc-Type: 4,ENCRYPTED DEK-Info: DES-EDE3-CBC,510F5F9D845B3CBB rst/cobTCt+ZfxX0loTX15jX5eNvS18vPy4ygQOr/+V1UYoNIn/i1dpNDtnqPQdb 1lc9keYOHyYzKS/2XCyMJhx+m648VTqrHRBT1k39etNRRH16FO8V0WP04BYn/W/q 2Rqg45kZqGrZIDy7mSb0/Mj/1+LX0+c/vhApv6KdWHULug/w0pc9i63V+sMq24Wu ZkQBOj/B+LMckhpS304Gjj4Lmev/cyj3SlFG2zany90FtWOmefihXpFgJfg2EiU8 UoYeKiM5jdEAXP9mfgH60s6UUdPjrKaBvUsbtWyzUDUcHheIAWTtAqmorr3anejw or20p67qI3J2LyXmgpxgSkswLZk6J5etLLfOMDZuqhViDx9EZ80bQ/dVf89w/78s hng5fWhNSmzpqlVPOl+QvQ26iV18HvQyN94qEE390rfMlqGLSyhrFf7zTZqWPe/E IRvf9GhmJq0iTsPW7VmpoBHirtCsZJpbl7YgwDU6JXD//ho8o0rEsUCvYXvLKSiz hGz9thMzmoOApciwZioO5mUmc9ZzTV0Z9ytsvAVRixu60VZUOJ64j/PsrCM40Nyu WsYxcUj2Zj1xD6+EmxnyUFvb/lxSfwlJ/CoD5rgY5qf02pfAjMdUwPaZSpvwGe4x pZ6VKQsVPyhVaWbM58Kcon4E00dvzze9PHtaAmhtmQo/9F/Y/Y4h1FnB51Ld8tu/ rK3zmt3vHqfvgFOSzQbFlIdJ+LJC+yFubmaPLFUurSuk3hts3mJZY1u0BI/CswsS TS965XbTJOVNNZQBqARtK2Hq5FhxsbNVS3CASvflO5fN1LpEmJ0ixWmnLX4NYu7P f7ePqZunRGaPdwAnw2ZpZV2xEPWxqIQyPtCbviAx+HtmO2p5i/bR0PDWSo7f3Wkz tGsJFmp7tRVGR/g9royFC6b86xZrKcowDj/ZvCMkqTxEQJYPgaJsZ0Rs5tAm3cDb bjJ2N193O9fQXL0jLp60E4ZCom82tF8R+zBAZKMqEWMFS6CLV6aMO1ycP2W2Zxbn 0zUOU6fDuBzCNuNCJez4lNcjtXfnN+Dxa9D3I/E88EVN1arsTMbAtMt97DDvGBPA /N58fWB4hOdQ9kwCHoh8nrKMde6phbX0KC5dutHnMtb13JqXOmIrzZhrXYy+Szcl qfmyRuJEPivY/Bu5NqwCOTUHWssk618WEcmxgD9Wigu9/BjySziZjxJtqG/krkMO 8R2w2KpCvr/GsOcm1Kr+6J7r9yyUslPxL6QRmZbgvFqQ4QyYeC8MoXbwrV43GwOq DQcH40yZ2ekOKOQZcB6V7pt/YUZtOvYuKHmTlqXQV5FdDzhQC5CHU5NqmTwb/F0/ HvRm18q2EcXOiQ5rqTXzcZ8WTl1xWqnL+yJQT/ODQ7rac25/hBZAFhfkl4/jfuMC GGPut9SyjnDfm0Wg0Sm8stwDqFhVQQIigBCCd7LIkYYwznTWZCU1v01bUvDhmmlU oZTkZ0Q8S4UGuxSA9sgS22tvA/dtyfERwIC6iDplFEfNSiamCKOUEdKCuIk8NsXz YsCN5KqiDk32mRfFSAR7ogQmbEYZFalF7UR2jR5ngVzItzcx0aazpA== -----END RSA PRIVATE KEY-----
2. I use Edge UI to paste it to the KVM:
3. I have these policies:
3.1. Get Secrets
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<KeyValueMapOperations mapIdentifier="KVM" async="false" continueOnError="false" enabled="true" name="GetKVM">
<DisplayName>Get Secrets</DisplayName>
<ExpiryTimeInSecs>3</ExpiryTimeInSecs>
<Scope>environment</Scope>
<Get assignTo="private.privatekey">
<Key>
<Parameter>RS256PK</Parameter>
</Key>
</Get>
<Get assignTo="private.privatekey_password">
<Key>
<Parameter>RS256PKPassword</Parameter>
</Key>
</Get>
<Get assignTo="private.secret_key">
<Key>
<Parameter>SecretKey</Parameter>
</Key>
</Get>
</KeyValueMapOperations>
3.2. Generate JWT
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<GenerateJWT async="false" continueOnError="false" enabled="true" name="Generate-JWT">
<Algorithm>RS256</Algorithm>
<IgnoreUnresolvedVariables>false</IgnoreUnresolvedVariables>
<PrivateKey>
<Value ref="private.privatekey"/>
<ID>123456789</ID>
<Password ref="private.privatekey_password"/>
</PrivateKey>
<Subject ref="google_tokeninfo.user_id"/>
<Issuer>apigee</Issuer>
<Audience ref="google_tokeninfo.audience"/>
<ExpiresIn>1800s</ExpiresIn>
<Id/>
<AdditionalClaims>
<Claim name="email" ref="google_tokeninfo.email"/>
<Claim name="azp" ref="google_tokeninfo.issued_to"/>
</AdditionalClaims>
<OutputVariable>apigee_jwt_token</OutputVariable>
</GenerateJWT>
3.3. Those policies are invoked from the Target Response PreFlow
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<GenerateJWT async="false" continueOnError="false" enabled="true" name="Generate-JWT">
<Algorithm>RS256</Algorithm>
<IgnoreUnresolvedVariables>false</IgnoreUnresolvedVariables>
<PrivateKey>
<Value ref="private.privatekey"/>
<ID>123456789</ID>
<Password ref="private.privatekey_password"/>
</PrivateKey>
<Subject ref="google_tokeninfo.user_id"/>
<Issuer>apigee</Issuer>
<Audience ref="google_tokeninfo.audience"/>
<ExpiresIn>1800s</ExpiresIn>
<Id/>
<AdditionalClaims>
<Claim name="email" ref="google_tokeninfo.email"/>
<Claim name="azp" ref="google_tokeninfo.issued_to"/>
</AdditionalClaims>
<OutputVariable>apigee_jwt_token</OutputVariable>
</GenerateJWT>
With all this I take necessary data from incoming Google tokens and generate my own JWT tokens.
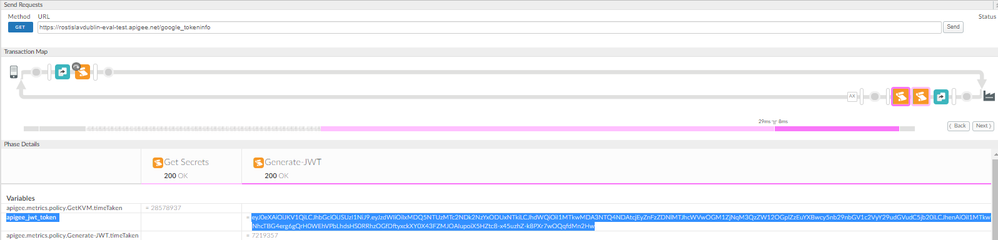
It works:
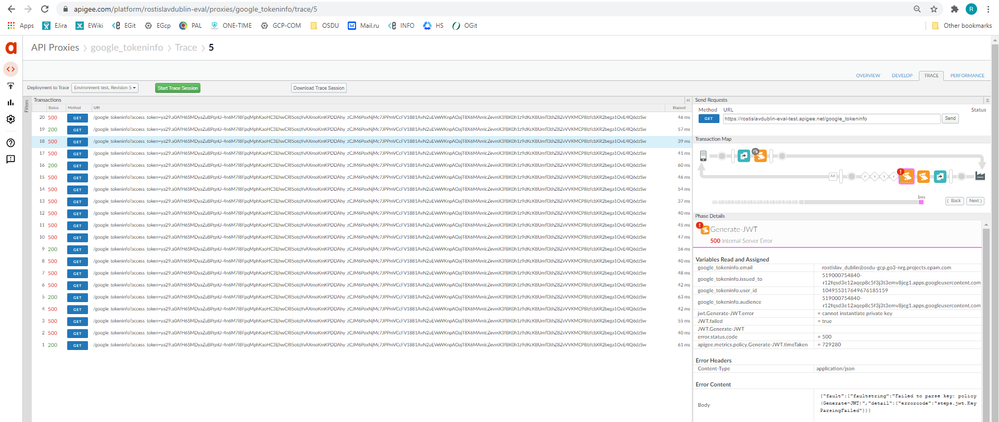
The question is:
Why does it fail in at least 75% cases?
Does it work as expected?
Only one of four requests succeeds:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is a new question. I suggest that you ask a new question, rather than posting your question as an answer to an 18-month old, already resolved question. The old question is similar, but not the same.
I have some insight and suggestions related to your question but won't respond further here. if you have a new question, please ask a new question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
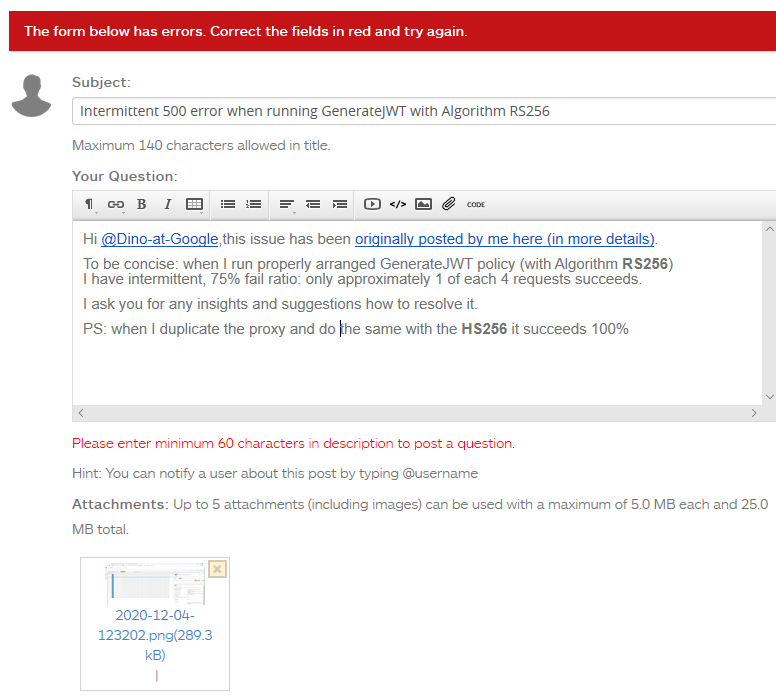
I am unable to publish a new question due to a error on your site.
Something is wrong, it rejects my attempts, I tried in several browsers and had the same error:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's unfortunate. I'm sorry.
We are having some problems with the site for some browsers. I have not been able to resolve that problem.
-
Analytics
497 -
API Hub
75 -
API Runtime
11,665 -
API Security
178 -
Apigee General
3,042 -
Apigee X
1,290 -
Developer Portal
1,911 -
Drupal Portal
43 -
Hybrid
463 -
Integrated Developer Portal
90 -
Integration
310 -
PAYG
13 -
Private Cloud Deployment
1,069 -
User Interface
77

 Twitter
Twitter